We are excited to announce the release of Aerospike 3.11. This release builds on our core mission of providing customers a highly scalable and performant key value database by adding hybrid memory improvements for greater performance and scale and crucial enterprise features such as transport encryption with key validation.
Hybrid Memory Improvements
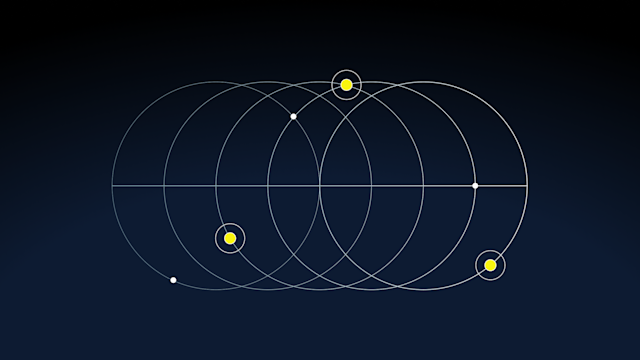
Aerospike provides the greatest level of performance on a wide variety of hardware, including the latest Intel CPUs and high capacity SSDs. Compared to other databases, Aerospike gains a significant total cost of ownership (TCO) advantage through both superior vertical scale via high performance multicore servers and horizontal scale via the ability to add nodes to clusters without operational downtime. In cases where each node may have upward of 1 billion objects, we are rolling out new optimizations that further improve performance.With the release of 3.11, we have greatly improved lock granularity through a mechanism known as sub-trees or sprigs. This innovative use of combining both trees and a hash table within our partition system provides the lowest DRAM use while also improving the extraordinary parallelism required by cutting edge Flash storage systems. The impact of background tasks such as node synchronization and object expiration also decreases. For more information on locks and sprigs, please see our configuration reference.
This internal change requires a rolling cold restart of the cluster, as the DRAM index layout has changed. Please see the cold start guide for operational details. This change is compatible between versions, so mixed version clusters operate correctly and require no client updates.Additionally, we found some multi-core scalability issues related to a third-party library (JEMalloc). By upgrading to a later version of JEMalloc (v4.2.1) and using a new lower level interface within JEMalloc, we have been able to greatly increase DRAM performance. In some cases, we have observed a 2x increase on multi-core systems.
TLS Transport Encryption
Although Aerospike is known for extraordinarily low latency and is thus often deployed within a single network security domain, some deployment environments need to extend across network security domains and require transport encryption. These features have been requested primarily by Aerospike’s financial services customers who use Aerospike for fast risk analysis, fraud detection and prevention, and account management. In partnership with our enterprise customers, we now support TLS 1.2 between client and server, as well as across geographic domains. Aerospike’s Enterprise Edition has contained access control since version 3.5.2.
Certificate based server validation is also supported. The client can be configured with a public key that allows cryptographic checking of the Aerospike cluster. By specifying the certificate of the cluster, you can avoid man-in-the-middle attacks within your infrastructure.
Our testing has shown that it is critical to leverage Intel’s in-CPU AES instruction set technology (available since 2010) and use GCM (Galois Counter Mode). Aerospike has found a dramatic performance difference between AES-256 in GCM mode and AES-256 in CBC mode. While GCM mode may result in a minimal (20%) performance degradation, CBC mode may result in a dramatic 5x degradation, depending on hardware. The Aerospike client and server can be configured to attempt to negotiate the higher performance ciphersuite, but If you intend to use Aerospike TLS with Java and need the highest level of performance, please contact Aerospike support.
Client support for TLS encryption is available in Java v3.3.1, C# v3.3.0 , C v4.1.0, and Go v1.24.0. You may have to first upgrade clients and then servers. Further clients will ship including this feature in the next six months.This feature is available in Aerospike Enterprise. Please see our feature guide and deployment guide for more information.
Client Improvements
Rust client: Aerospike has introduced a beta version of a client for the Rust language. Please see the github repository for more information.IPv6: This functionality, introduced in the server in release 3.10, is now available in the following clients: Java, C, C#, Go, and Node.SortedMap: Initially released in 3.10, SortedMap functionality is now improved and available in General Availability. Clients supporting this functionality include Java, C#, C, Node.js, Go, Python, and Ruby.
Other Notable Improvements and Fixes
Release 3.11 incorporates other improvements such as:
Update without modifying TTL: To allow easier programming when a database record needs to be written without changing a previously written TTL (introduced 3.10.1).
Conflict resolution: In some cases when using generation-based conflict resolution, roll over of the generation count could lead to inaccurate comparisons during data resynchronization. The algorithm now used during data resynchronization is a pure greater-than comparison (similar to pre 3.6).
Performance: In some cases, transactions would attempt to read and resolve copies of data that did not exist. Now, data is only resolved when explicitly configured to do so.
Operations: When synchronizing data after a cluster change, you can limit the number of servers that can simultaneously transmit to a single server, resulting in smoother processing after a cluster change.
Tuning: It is now possible to change the number of transaction processing threads on the fly by changing the “transaction-threads-per-queue” variable. This change is applied without a restart.
Please see the release notes for more detailed information.
What’s Next?
In future releases, we intend to introduce several new features. Please consider the below list as a preview, not a commitment!
Improved Paxos clustering algorithms for larger clusters and greater stability in public cloud environments
Addition and removal of namespaces without downtime
Incremental backup and restore
If you’d like to download Aerospike 3.11, visit our download page.As always, we look forward to your input and help to continue to improve and enhance Aerospike. Feel free to contribute your feedback, ideas, and questions to our user forum, file Github issues, or create a pull request for the next great feature you’d like to contribute to the Aerospike user community!
Keep reading

Apr 28, 2026
Aerospike Voyager: From first connection to production code
Apr 28, 2026
Introducing the Aerospike Java and Python SDKs: A generational upgrade to building on Aerospike

Apr 22, 2026
Aerospike vs. Cassandra: Databases don’t need to go down to break your application

Apr 16, 2026
Introducing Aerospike 8.1.2: Making nested data queries fast and easy to write
